 Despite the many advantages provided by cloud computing technology, the rate of adoption among large enterprises has been surprisingly slow, especially when compared to the way SMEs have embraced the technology. The main reason for the slow rate of adoption is the fact that migrating to the cloud would generally require the discarding of many legacy hardware and applications that no longer have any purpose.
Despite the many advantages provided by cloud computing technology, the rate of adoption among large enterprises has been surprisingly slow, especially when compared to the way SMEs have embraced the technology. The main reason for the slow rate of adoption is the fact that migrating to the cloud would generally require the discarding of many legacy hardware and applications that no longer have any purpose.
SMEs and new startups don’t have many of either types of legacy infrastructure pieces, and sometimes were able to start their operations on the cloud, but large enterprises are burdened with legacy infrastructure that cost hundreds of thousands of dollars in hardware and software, not to mention that discarding them and moving to the cloud would result in disruptions to their operation, further costing them money.
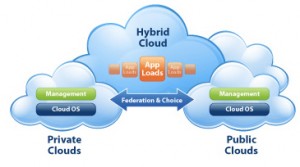
The solution adopted by many large enterprises, particularly ones who felt that they are getting left behind by companies that have already moved to the cloud, is to deploy a hybrid cloud model, which is basically using their legacy infrastructure alongside a public cloud service, such as Amazon’s Simple Storage Service or Google Drive. The main benefits of a hybrid cloud consist of gaining the advantage of the technology, such as flexibility, agility, and cost-efficiency without sacrificing their expensive legacy infrastructure nor requiring massive downtimes just for the migration.
Unfortunately, many large enterprises are still on the fence even with the benefits provided by a hybrid cloud deployment, mainly due to security concerns. The migration of resources to the hybrid clouds increases the complexity of software and configuration, not to mention other security issues related to managing the communication link between different sites during the delivery of IT infrastructure from the cloud to the enterprises. Firewall rules, and incompatible network policies.
Understanding Different Types of Cloud Delivery Models
See Security Challenges in Hybrid Cloud Infrastructures by Koushik Annapureddy
Software as a Service (SaaS) – with SaaS, the enterprise hosts and operates their application while users access it over the Internet. The main benefit of SaaS is that there is no need to buy any software licenses or equipment for the application. Most of the time, the only cost involves paying for the use of the software application. Some examples of SaaS are the popular webmails Gmail, Yahoo Mail, and even Google Calendar.
Platform as a Service (SaaS) – as the name implies, PaaS provides an entire platform that can be used for building and running custom applications, therefore reducing the complexity and cost involved with application development, which used to include hardware, database, operating system, middleware, and other software. PaaS allows enterprises to build applications without a single tool on their local workstations. PaaS also greatly reduces the time needed to build applications compared to conventional Java or .Net methods.
Infrastructure as a Service (IaaS) – with IaaS, the entire IT infrastructure is migrated to the cloud, and the responsibility of tackling issues and managing everything from server configuration, software patching, application deployment and everything in between is in the care of the cloud provider. The main benefit of this type of delivery model is that it saves a lot of money and effort that the enterprise would otherwise have to shoulder. In most cases, enterprises no longer need an entire department and office space just for the maintenance of their infrastructure, as it is already shouldered by the cloud provider.
Different Cloud Models
Regardless of service model delivery, there are also four different deployment models used based on the requirements of the enterprise, such as:
Public Cloud – this is a cloud model usually offered by large service providers to the general public over the internet, usually in the form of applications and storage. Most examples of the public cloud are either offered for free or through a pay per use model. Examples include Amazon’s Elastic Compute Cloud, Google AppEngine, and Windows Azure Services Platform.
Private Cloud – this type of cloud is basically the same as a public cloud in terms of operation, but the resources are operated exclusively for a single organization. The service provider can be a third party or the organization itself. This type of cloud is used by private organizations for providing hosted services to people behind a firewall, and is preferred by enterprises who want absolute control over their data.
Community Cloud – this is a type of cloud model wherein several organizations with common requirements share a single cloud infrastructure. It is preferred by organizations that don’t want to depend on major cloud vendors due to privacy, efficiency, and security concerns.
Hybrid Cloud – as the name implies, a hybrid cloud is the combination of two or more clouds (private, community, and public). It’s main feature is that it uses existing resources on premises and combines it with cloud functionality. The main benefit of this model is that it allows enterprises to still have control over their data while enjoying some of the benefits of the cloud.
Challenges and Insights
Many large enterprises these days use hybrid clouds, in the sense that they place their applications on site and partly in the cloud. Due to the importance of data in many enterprises, the ability to monitor, protect, and enforce access permissions is of utmost importance. The tiniest of holes in the security is unacceptable and many complex systems and solutions are devised in order to protect the integrity of their data security.
Aside from protection of their data, enterprises also need to comply with regulations that pertain to data governance. Moving the data to the cloud makes them lose governance over their own data set. Once they move the data to the cloud, its safety becomes the responsibility of the cloud service provider.
Koushik Annapureddy of the Aalto University published a study conducted by Symantec, around 83% of enterprises rated security as an important criteria to be considered when it comes to hybrid clouds. 79% cited backup and recovery and 76% believed continuous data protection is included in the top priorities.
Challenges Associated with Moving Components to a Hybrid Cloud
- Security of Data – Annapureddy assessed that despite the cost efficiency and agility provided by hybrid clouds, many enterprises refuse to commit to it because they trust existing internal security measures over the ones employed by cloud service providers. They fear that moving to the cloud sacrifices a lot of control, and that the confidentiality of their data will be violated as the data present in the cloud can be leaked or tampered with, either intentionally or by accident.
- Adjustments and Reprogramming – there are a lot of concerns generated when migrating components from on-site to the public cloud, such as component placement, as many applications used by enterprises today have complex interactions and inter-dependencies, and moving them to the cloud without any preparations could result in them being broken and unable to work.
- Integrity of Applications – Microsoft in its White Paper titled Security Issues in the Hybrid Cloud stated that one of the main priorities of cloud service providers is standardization of APIs, so that they can easily accommodate many different subscribers with different needs while remaining agile enough to roll out patches and upgrades when needed. However, this standardization could introduce security risks that are also standardized among all subscribers, so that a security hole on one enterprise could result in vulnerabilities for all subscribers. Many enterprises fear this situation, wherein their data could get compromised through no fault of their own.
Solutions
See Security Challenges in Hybrid Cloud Infrastructures by Koushik Annapureddy
- Amazon VPC – developed by Cloud giant Amazon, it stands for Virtual Private Cloud, is basically a means for subscribers to create their own virtual cloud from within Amazon’s public cloud. The VPC uses a VPN connection between enterprise IT infrastructure and the enterprise virtual cloud via an IPsec tunnel mode, which protects data from tampering and eavesdropping.
- Open VPN – this is an open source VPN solution meant to provide secure data exchange between networks. It uses OpenSSL-based encryption for securing the data and uses a secure tunnel for data exchange between the enterprise’s infrastructure and the cloud. All communication is encrypted via the OpenSSH protocol. It also supports multiple ways of authenticating the cloud and enterprise before establishing a secure connection. These include smart cards, verifying certificates, and username/password-based credentials as well as firewall access control policies.
- Data Encryption – Intel UK identified encryption as a common solution for addressing concerns over confidentiality, integrity, and security. Enterprises must encrypt their data and communications in order to protect against hacking, eavesdropping, and tampering attempts. The catch is that managing the encryption mechanism in the cloud will require a lot of overhead in management and configuration. All of the data present in the cloud must be encrypted and should require a decryption key from the enterprise. Poor configuration and management can result in key exposure, which will give intruders free access to all the sensitive data.
Conclusion
Cloud Computing Technology has matured in a way that it becomes a necessity for businesses and organizations these days, but it is still up to the enterprises to decide if the benefits it providers are worth the security challenges they must hurdle. As provided above, there are ways to address the concerns as long as they know what they want and take steps to ensure that they apply the countermeasures correctly. In a sense, Hybrid cloud works under the same principles.